MOSQUITO Attack Uses Headphones, Speakers, and Microphones to Leak Data Over Ultrasonic Frequencies
A cybersecurity research group in Israel has recently published a paper in which they describe the MOSQUITO attack—an attack that can reverse speakers and microphones in air-gapped computers, and use them to send data to one another using ultra-sonic frequencies.
The MOSQUITO attack utilizes jack retasking to leak data over ultrasonic frequencies—and can be transferred between air-gapped computers.
A cybersecurity research group in Israel at Ben-Gurion University of the Negev has recently published a paper in which they describe the MOSQUITO attack, which can reverse speakers and microphones in air-gapped computers and use them to send data to one another using ultrasonic frequencies.
As described in the paper on the MOSQUITO attack, the attack requires malware to be installed on a system to be effective. However, an infected USB stick or email is all it would take to turn a computer with a set of headphones, speakers, or microphones casually plugged-in into communication devices between air-gapped computers that are not connected in any other way.

A panda graphic transferred between air-gapped computers. Screenshot courtesy of Cyber Security Labs, Ben Gurion University
The hack requires three steps:
- Jack retasking
- Synchronization
- Transmission/reception
Of course, the attack also begins initially with the infection of two computers that communicate covertly with one another.
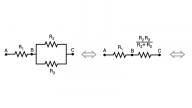
Jack Retasking
The first step, “jack retasking”, is based on a software feature that can reprogram an audio port to act as input or output and can be found on most sounds cards. Fundamentally speaking, microphones and speakers are just the reverse of one another: one detects air-pressure on a diaphragm and converts it into electrical-pulses (a microphone), and the other does the opposite and creates sound by pulsating a diaphragm using electrical signals (speakers). The researchers in their paper mention that, although it is possible to reverse a speaker to act as a microphone, since it’s not intended to act as one the quality of the audio it picks up will not be as good. As well, this only works with passive speakers, or speakers that do not have an amplifier between the audio jack and the speaker. Headphones, however, are passive speakers and can be reversed to act as microphones.
Synchronization
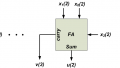
Once the jack retasking is complete, the two infected computers will initiated a protocol to synchronize with one another. The researchers implement their own, light version of an acoustic communication protocol to establish synchronization between two computers, which uses a 46-bit message frame containing the message preamble, payola, and CRC. The protocol also has seven control messages including: DISCOVERY, ACQUIRE, RELEASE, ACK_OK, RETRANSMIT, BITRATE_INC, and BITRATE_DEC. When transmitting the DISCOVERY message, the computer will do so at random intervals over a 5000ms time frame until it receives a response. The transmission is randomized so that if another computer is also transmitting, they don’t accidentally synchronize a collision.

Image courtesy of the BGU Cyber Security Research Center.
Transmission/Reception
Finally, data exchange can begin. Both computers will exchange binary data by switching their speaker or microphones between listening and sending, using ultrasonic pulses in the 18-24kHz range, which most adult humans can not hear.
Demonstrating the MOSQUITO Attack
The demonstration of the attack in the video above is carried out over three modes: speaker-to-speaker, speaker-to-headphones, and headphones-to-headphones.
In the video, the team succeeds in transmitting data between air-gapped computers at a rate of 10-166 bit/sec, and up to a distance of eight meters away when using speakers, or three meters away when using headphones.
Risks and Countermeasures
Some of the suggestions for countermeasures against such an attack include using ultrasonic frequency jammers, disabling jack retasking on computer sound cards, and strictly using one-way, active speakers so that they cannot be reversed.
Protecting against such attacks might not be necessary for an everyday computer user’s personal laptop. In work environments, however, where there is sensitive information on the computers in question, the risk may be higher. If an isolated computer is infected and it is able to synchronize with another computer that has an Internet connection, information could be leaked—albeit, slowly and probably with a lot of effort.
Featured image courtesy of the BGU Cyber Security Research Center.

 Facebook
Facebook Google
Google GitHub
GitHub Linkedin
Linkedin









Very interesting from an academic viewpoint, but I hope that no-one was paid for conducting this research !
At that data rate just how long would it take to ‘borrow’ something useful from a hacked computer ?
Yea, this could be really useful! Send out commands to all the mosquitoes in the room to attack humans NOW! He, he, he!