DeepCover: Maxim Integrated’s Secure Authenticator with a Host of Security Services
Maxim Integrated recently announced the DS28E36 IC, which is a secure authenticator that uses Maxim's DeepCover embedded security solutions.
Maxim Integrated recently announced the DS28E36 IC, which is a secure authenticator that uses Maxim's DeepCover embedded security solutions.
The security of connected devices, such as the plethora of IoT widgets that are seemingly everywhere, should not be overlooked given the ever-increasing sophistication of dedicated hackers. The DS28E36, from Maxim Integrated, is a “secure authenticator” that helps to protect IoT nodes by providing “cryptographic tools.”
According to Maxim's article entitled "DeepCover Embedded Security Technology", their secure authenticators "implement advanced physical security" to provide protections covering IP, clone prevention, and peripheral authentication. Seems impressive. What's not impressive, or rather what's a bit surprising, at least to me—although I'm no expert in secure authenticators—is the rather large package.
According to the DS28E36’s datasheet, this 6-pin device (only five of the six pins are made available to the designer) measures in at 3×3mm (see the figure below). But perhaps larger IC packages are a requirement for such apparently impressive single-chip security devices. A quick glance at the datasheet’s list of “benefits and features” certainly does indicate that there is a lot going on inside this device.
_pinout.jpg)
Figure 1. The DS28E36 comes in a rather large package, though it would probably seem small if we could see all the transistors in there.... Diagram taken from the datasheet (PDF).
An Overview of DeepCover
DeepCover embedded security solutions, such as the DS28E36, attempt to offer the most secure key storage possible by concealing sensitive information under multiple layers of sophisticated security measures. Such safeguards include the implementation of both invasive and noninvasive countermeasures such as active die shield, encrypted storage of keys, and algorithmic methods. To this end, the DeepCover secure authenticator provides a set of cryptographic tools (listed below) that originate from integrated asymmetric (ECC-P256) and symmetric (SHA-256) security functions.
- The device integrates a FIPS/NIST true random number generator (RNG).
- 8 kbits of secured EEPROM are used; they are divided into two 4-kbit regions:
- One region is reserved for user-programmable and configurable memory.
- The other 4-kbit region is used for registers.
- A decrement-only counter.
- Two pins of configurable GPIO.
- A unique 64-bit ROM identification number.
_block_diagram-1.jpg)
Figure 2. A simplified block diagram of the DS28E36 DeepCover secure authenticator, from the datasheet (PDF).
1-Wire Communications
Communications to and from the DS28E36 occur over a single-contact communication bus called 1-Wire.
A significant portion of the DS28E36 datasheet is dedicated to 1-Wire communications; see the sections entitled 1-Wire Bus System and 1-Wire Signaling and Timing. And if you're not too familiar with this 1-Wire protocol, it may be worth your time to review this material because, as pointed out in the datasheet, "The DS28E36 requires strict protocols to ensure data integrity."
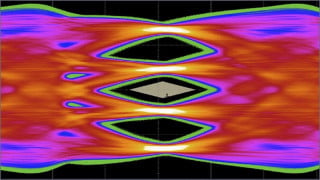
The diagram below depicts the "time slots" required for both the reading and writing of data using the 1-Wire bus.
_timing_diagrams.jpg)
Figure 3. 1-Wire timing diagrams, from the datasheet (PDF).
Decrement Counter
In applications that have limited-use requirements, device usage can be tracked by means of a nonvolatile decrement-only counter. This 17-bit one-time settable counter—which means that it can only be initialized or written to one time—is decremented by an external controller, and once the count reaches zero no additional decrements are possible.
This is a good time to clarify something: The DS28E36 is not some sort of cryptographic processor (such as the Microchip part discussed in this article), and it is not any other type of standalone cybersecurity solution. It’s an add-on, i.e., something that you incorporate into a design so that the overall system can benefit from the DS28E36’s security features. Since most embedded devices are managed by a microcontroller, the standard arrangement here is a 1-wire bus in which the bus master is a microcontroller and the DS28E36 is a slave (or one of the slaves, since the 1-wire interface supports multiple slave devices).
There is undoubtedly something clever about a serial communication bus that uses only one wire yet supports bidirectional communication. Nevertheless, it’s fair to recognize that the 1-wire bus could complicate your design or even dissuade you from using this part, because this interface is much less common than, say, I2C or SPI, and because it doesn’t appear to be particularly straightforward.
Evaluation Kit
A chip with this level of complexity is always easier to test drive when you can start with some hardware designed by the experts, so definitely take a look at the DS28E36’s evaluation kit if you’re trying to decide if this device is the answer to your IoT security concerns.
_Eval-kit.jpg)
Figure 4. The DS28E36 evaluation system. Image taken from the eval kit's datasheet (PDF).
Have you had a chance to use this new authenticator IC or its evaluation kit? If so, leave a comment and let us know what you think.

 Facebook
Facebook Google
Google GitHub
GitHub Linkedin
Linkedin