A Critical DRAM Fault Poses a Looming Threat to CPU Security
Rowhammer attacks are just one type of affront to DRAM security. Now, a team at ETH Zürich has uncovered an even more insidious threat to CPU memory.
Researchers at ETH Zürich claim there are major security threats to dynamic random-access memory (DRAM) devices that have been overlooked.

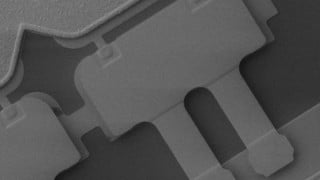
The security vulnerabilities could threaten computer memories. Image used courtesy of ETH Zürich
On a personal laptop or smartphone, software protection like anti-virus can usually keep memory attacks at bay. But now, a team of researchers led by Kaveh Razavi at ETH Zürich, along with support from the Vrije Universiteit Amsterdam and Qualcomm Technologies, recently discovered a critical weakness in standard DRAM memory that leaves it unguarded against certain Rowhammer attacks.
Rowhammer Attacks: A Modern Day Threat to DRAM
A Rowhammer attack refers to a security exploit in which a bad actor repeatedly activates or "hammers" a row of memory. These continual attacks create bit errors in a neighboring row, which the attacker can then use to tap into a computer system.
Leaking charges in the DRAM memory cells enables attackers to induce bit flips within the memory. This leakage stems from a single capacitor-transistor pair used to store and access bits of information; once a capacitor loses too much charge, it becomes hard to decipher if the stored data is a 0 or 1.

Structure of a DRAM device. Image used courtesy of ETH Zürich
To combat a Rowhammer memory attack, chip manufacturers have attempted to implement mitigation measures inside conventional DRAM modules, but these measures have had little success in the last ten years.
ETH Zürich's Designs the Blacksmith Attack
ETH Zürich researchers have found that modifying a standard Target Row Refresh (TRR) mitigation could be the solution chip manufacturers have been searching for. TRR is composed of circuits built into the memory. These circuits can detect out-of-the-norm, high activation frequencies to estimate an attack's location.
ETH Zürich’s modification known as Blacksmith involves a non-uniform and frequency-based solution that will identify potential faults that TRR overlooks. Most TRR mitigation routes are expensive to be placed on hardware and still permit security attacks.
The researchers used complex hammering patterns, known as a Blacksmith attack, on DRAM devices to expose a number of bit errors. These significant findings received a Common Vulnerabilities and Exposures (CVE) number of 9 out of 10 from the Swiss National Cyber Security Centre (NCSC), indicating the severity of this hardware vulnerability.
Building DRAM's Immune System
When DRAM faults are identified, the read and write data appears to come from an incorrect address, and the data is corrupted in the process. Data can also be corrupted without a write/read action, leaving the memory unchanged. ETH Zürich’s Blacksmith adds a control circuit that will refresh the anticipated memory cell row and prevent possible bit errors from occurring.

Standard Rowhammer access patterns can affect the adjacent rows by increasing charge leakage before it has a chance to refresh, losing any stored data. Image used courtesy of ETH Zürich
ETH Zürich researchers conducted testing on 40 DRAM devices from Samsung, Micron, and SK Hynix to observe Rowhammer single, double, and n-sided patterns, showcasing the intensity of accessibility from non-uniform patterns.
The researchers completely bypassed TRR by seeking non-uniform patterns. This is because their method lacked frequency, amplitude, and phase parameter control. Over a 12-hour test, the Blacksmith “fuzzer” triggered thousands of bitflips in all 40 DRAM devices.
The ETH Zürich study yielded a sophisticated way to induce bit errors. The next step, now, is for chip manufacturers to update mitigation measures for next-gen DRAM devices.

 Facebook
Facebook Google
Google GitHub
GitHub Linkedin
Linkedin