Side-Channel Attack Threatens Safari Browser Through Apple Processors
An international team of researchers recently found that Apple’s Safari web browser is still susceptible to a Spectre attack called iLeakage.
When the Spectre and Meltdown security vulnerabilities hit the news headlines in 2018, they caused alarm for anyone operating a personal or enterprise computer. While Meltdown exclusively affected Intel processors, Spectre affected many Intel, Arm, and AMD processors. By exploiting speculative execution—a mechanism by which a processor loads instructions into the instruction pipeline before a branch target is determined—hackers could access extremely sensitive data stored in the computer’s memory.
Researchers from Ruhr University Bochum in Germany, Georgia Tech, and the University of Michigan recently demonstrated how the ramifications of Spectre and Meltdown still echo today.

Apple's Safari browser is susceptible to a certain Spectre attack discovered by an international team of researchers. Image used under Adobe Stock license
The team published a study describing how they exploited a hardware vulnerability using Apple's Safari browser to tap into emails, passwords, and even location data. Apple has attempted to address this side-channel attack, dubbed "iLeakage," through software updates, but some critical security concerns remain unresolved.
Spectre: A Unique Side-Channel Attack
To understand the working principle behind the most recently exposed Spectre attack, we must first discuss the implicit weaknesses of modern computer architectures. These architectures use cache memories to reduce the latency of memory accesses. When a core needs to access a memory location for the first time, it reads from the main memory. After a read from the main memory, that memory's location and its contents are cached for faster access in the future.

The three types of cache. Image used courtesy of Tech4Gamers
While caching reduces memory access latency, it can be exploited by malicious actors. Before a hacker can access sensitive data, they need to understand whether it is located in the main memory or a cache. One version of the Spectre attack trains the processor to mispredict the result of a branch instruction and speculatively load a piece of code known as the gadget. The attacker first runs code to load the address of the gadget code in the branch target buffer (BTB) of the processor. The BTB maps the source address to the destination address for branch instructions to speed up the processor's branch prediction capabilities.

Pseudocode showing memory access time measurement. Image used courtesy of RedHat
Once the BTB is mistrained to hold the gadget code address for a particular branch instruction, the processor speculatively loads the gadget code into the instruction pipeline. The gadget code execution is then present in the cache. As a result, the attacker can extract the sensitive data from the cache once the gadget code completes.
Safari Browser Remains Susceptible to Spectre Attacks
Since the methodology behind Spectre and Meltdown attacks was made public, developers have made many efforts to mitigate the potential for such attacks. Intel developed microcode instructions to deter the flavor of Spectre mentioned earlier. This method prevented user code from affecting the branch prediction outcomes stored in the BTB of more privileged code. As a result, the speculative execution of gadget code could not be induced in the same way.
Like other web browsers such as Chrome and Firefox, Apple's Safari web browser also has various mitigation techniques to prevent side-channel attacks like Spectre. One of the key ways Safari mitigates side-channel attacks is to spawn a new process for each tab opened in the browser. In contrast to a thread, a process contains its own address space separate from other processes.

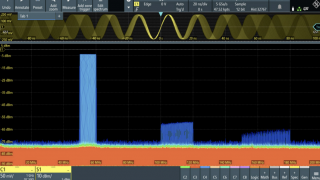
iLeakage can retrieve information with high accuracy. Image used courtesy of iLeakage.com
The joint U.S.-German research team discovered that this isolation can be easily bypassed using the Javascript API, forming the beginning of the sophisticated iLeakage attack. To trigger this attack, the victim must click on a malicious link and open a new webpage. Subsequently, the victim’s personal information can be read through a Spectre attack.
From a software perspective, iLeakage manipulates Javascript primitives to bypass many of Safari’s built-in safety mechanisms, such as type confusion and value poisoning. From a hardware perspective, it allows the attacker to mistrain the branch predictor of the processor, gain access to evicted cache lines, and consequently, gain access to the data inside them.

 Facebook
Facebook Google
Google GitHub
GitHub Linkedin
Linkedin